Ledger Login Explained — Secure Access, Hardware Authentication, and Self-Custody Protection
Discover how Ledger login works, why hardware wallets keep private keys offline, how cold storage defends your assets, and how to avoid scams using concepts like cryptographic signing, blockchain verification, and secure elements.
Understanding the Importance of a Safe Ledger Login
In the world of self-custody, security begins with the login process.
Ledger devices separate the interface from the signing mechanism — a design that ensures private keys never touch the internet.
Attackers know this, so they attack the user instead by creating fake portals, clone websites, or messages demanding sensitive information.
By learning the correct workflow and the reasoning behind it, you gain confidence in concepts such as private keys, transaction signatures, cold storage, deterministic wallets, and blockchain immutability.
This article walks you through the process step by step while building a deeper understanding of Ledger’s security architecture.
Ledger devices separate the interface from the signing mechanism — a design that ensures private keys never touch the internet.
Attackers know this, so they attack the user instead by creating fake portals, clone websites, or messages demanding sensitive information.
By learning the correct workflow and the reasoning behind it, you gain confidence in concepts such as private keys, transaction signatures, cold storage, deterministic wallets, and blockchain immutability.
This article walks you through the process step by step while building a deeper understanding of Ledger’s security architecture.
What Ledger Login Actually Does
During a login session:
This architecture protects users from malware, viruses, keyloggers, and remote attacks because signing requires physical interaction.
- Ledger Live displays balances and transaction history
- The hardware wallet stores the cryptographic keys offline
- Authentication happens on the physical screen
- Signing is performed inside the secure chip
This architecture protects users from malware, viruses, keyloggers, and remote attacks because signing requires physical interaction.
A Real-World Example: The Fake Login Trap
Julia clicked a page that looked identical to Ledger’s dashboard.
It requested her recovery phrase under the pretense of “security verification.”
Because she knew that recovery phrases must stay offline, she immediately abandoned the site.
This is a common tactic used by scammers worldwide — cloned interfaces paired with pressure tactics.
**Understanding the true login flow removes the uncertainty and blocks many attacks before they succeed.**
It requested her recovery phrase under the pretense of “security verification.”
Because she knew that recovery phrases must stay offline, she immediately abandoned the site.
This is a common tactic used by scammers worldwide — cloned interfaces paired with pressure tactics.
**Understanding the true login flow removes the uncertainty and blocks many attacks before they succeed.**
Ledger Login — Step-by-Step Secure Flow
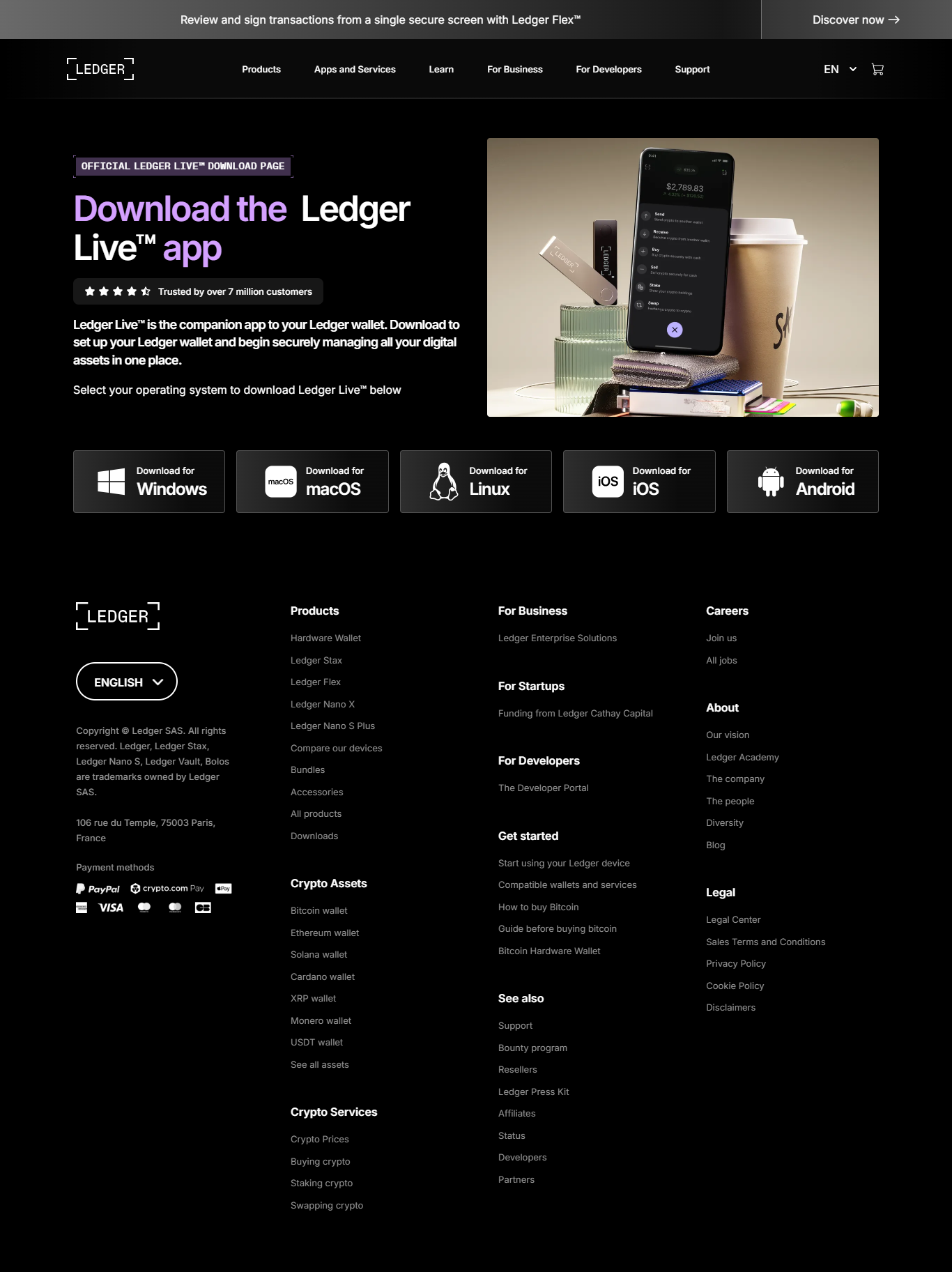
1. Install Ledger Live From the Official Source
Fake sites often appear above the official one in search engines.
2. Open the Application
Ledger Live acts as a viewer, not a keyholder.
3. Connect Your Ledger Device
USB or Bluetooth depending on model.
4. Enter Your PIN Directly on the Device
This PIN never appears on your screen, protecting it from digital threats.
Core Security Mechanisms of Ledger
Ledger wallets integrate:
Concepts such as public-key cryptography and hierarchical deterministic wallets (HD wallets) further strengthen the structure.
- Secure element chips resistant to tampering
- Offline cryptographic signing
- Physical confirmation screens
- Isolated cold storage environments
Concepts such as public-key cryptography and hierarchical deterministic wallets (HD wallets) further strengthen the structure.
Security Comparison of Wallet Types
| Wallet | Security | Key Control | Best For |
|---|---|---|---|
| Ledger Hardware Wallet | Very High | User | Long-term storage |
| Mobile Wallet | Medium | User | Everyday use |
| Exchange Wallet | Low | Exchange | Trading |
Ledger Safety Checklist
✔ Always use official software
✔ Never type your recovery phrase online
✔ Keep backups offline
✔ Verify every transaction on the device
✔ Avoid unsolicited support links
✔ Keep firmware updated
✔ Never type your recovery phrase online
✔ Keep backups offline
✔ Verify every transaction on the device
✔ Avoid unsolicited support links
✔ Keep firmware updated
Frequently Asked Questions
1. Does Ledger Live store private keys?
No — keys stay inside the hardware wallet.
2. Is a password required?
Only the PIN on the physical device.
3. Can Ledger be compromised?
Not in a way that reveals keys due to offline signing.
4. Does it support many assets?
Yes — thousands across many chains.
5. What if I lose my device?
Restore using your recovery phrase on a new Ledger.
No — keys stay inside the hardware wallet.
2. Is a password required?
Only the PIN on the physical device.
3. Can Ledger be compromised?
Not in a way that reveals keys due to offline signing.
4. Does it support many assets?
Yes — thousands across many chains.
5. What if I lose my device?
Restore using your recovery phrase on a new Ledger.
Conclusion — Secure Ledger Login Is the Foundation of Self-Custody
Ledger login combines an intuitive interface with powerful hardware authentication.
Because private keys remain offline, and because signing requires physical approval, the risk of remote theft drops dramatically.
Users who follow official procedures, avoid online recovery phrase requests, and verify transactions on-screen benefit from a robust defense powered by cold storage, secure elements, and cryptographic verification.
Stay cautious, follow the authentic flow, and keep your assets firmly under your control.
Because private keys remain offline, and because signing requires physical approval, the risk of remote theft drops dramatically.
Users who follow official procedures, avoid online recovery phrase requests, and verify transactions on-screen benefit from a robust defense powered by cold storage, secure elements, and cryptographic verification.
Stay cautious, follow the authentic flow, and keep your assets firmly under your control.